How does a proxy work?
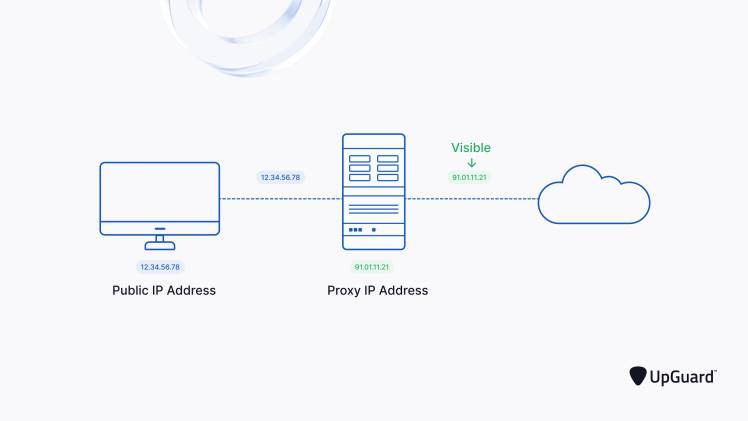
A proxy is a server that acts as an intermediary between your computer and the internet. When you connect to the internet, you do so through your ISP (internet service provider). However, when you use a proxy server, your connection goes through the proxy server first.
The proxy server then makes the request on your behalf and returns the response to you. This means that your IP address is hidden from the sites you visit, and it can also be used to bypass restrictions such as geo-blocking. Visit here for more descriptions of Exipure
Proxy servers can be used for both legal and illegal purposes. For example, they can be used to improve performance or security, or to access blocked websites. However, they can also be used for malicious purposes, such as stealing personal information or distributing malware.
Which proxy is safest?
There are many different types of buy usa proxy servers available and it can be tricky to know which one is the safest. Here are a few things to consider when choosing a proxy server:
-The level of security offered: Some proxy servers offer more security than others. Consider the type of data you will be sending through the proxy and choose one that offers the appropriate level of security.
-The location of the server: If you are concerned about your privacy, choose a proxy server that is located in a country with strong privacy laws.
-The speed of the connection: Some proxy servers can slow down your connection speed. If speed is important to you, make sure to choose a fast proxy server.
Are proxy sites safe?
When it comes to online privacy, one of the first questions that comes to mind is: are proxy sites safe? There are a lot of people who use proxy sites to browse the web anonymously and keep their personal information private. But is this really the best way to stay safe online?
Here’s a look at what proxy sites are and how they work, as well as some of the risks associated with using them. Buy uk proxy server is a computer that acts as an intermediary between your device and the internet. When you connect to a proxy server, your traffic is routed through that server before it reaches its destination. This means that anyone monitoring your traffic will only see the IP address of the proxy server, not your actual IP address.
Can a proxy be hacked?
Proxies are often used to protect a user’s identity and location. But what happens when a proxy is hacked? Can a hacker gain access to the user’s information?
It is possible for a hacker to hack into a proxy server. By doing this, the hacker can gain access to the user’s information. This includes the user’s IP address, location, and any other personal information that was set up in the proxy.
While it is possible for a hacker to hack into a proxy, it is not an easy task. The hacker would need to have a lot of knowledge about how proxies work. They would also need to have access to the server that the proxy is hosted on. If you are using a proxy to protect your identity and location, you should make sure that the proxy is secure.
What proxy do hackers use?
A proxy server is a computer that acts as an intermediary between your computer and the internet. Hackers use proxy servers to anonymously route their internet traffic through, making it difficult to trace their activities back to them.
There are many different types of proxy servers available, and hackers will often use multiple proxies in order to further hide their tracks. Some of the most popular types of proxies used by hackers include public proxies, web-based proxies, and VPNs.
Hackers will often use multipleproxy servers in order to further hide their tracks. By doing this, they can make it very difficult for anyone to track their activities back to them. If you’re concerned about being tracked online, you can use a proxy server yourself in order to stay anonymous.
Final Thought:
A proxy works by forwards internet requests from a user to the desired website. This process is done through an intermediate server, which acts as a middleman between the user and the website. By doing so, the user’s IP address is hidden from the website, providing anonymity. Additionally, proxies can also be used to bypass restrictions or filters that may be placed on certain websites.



